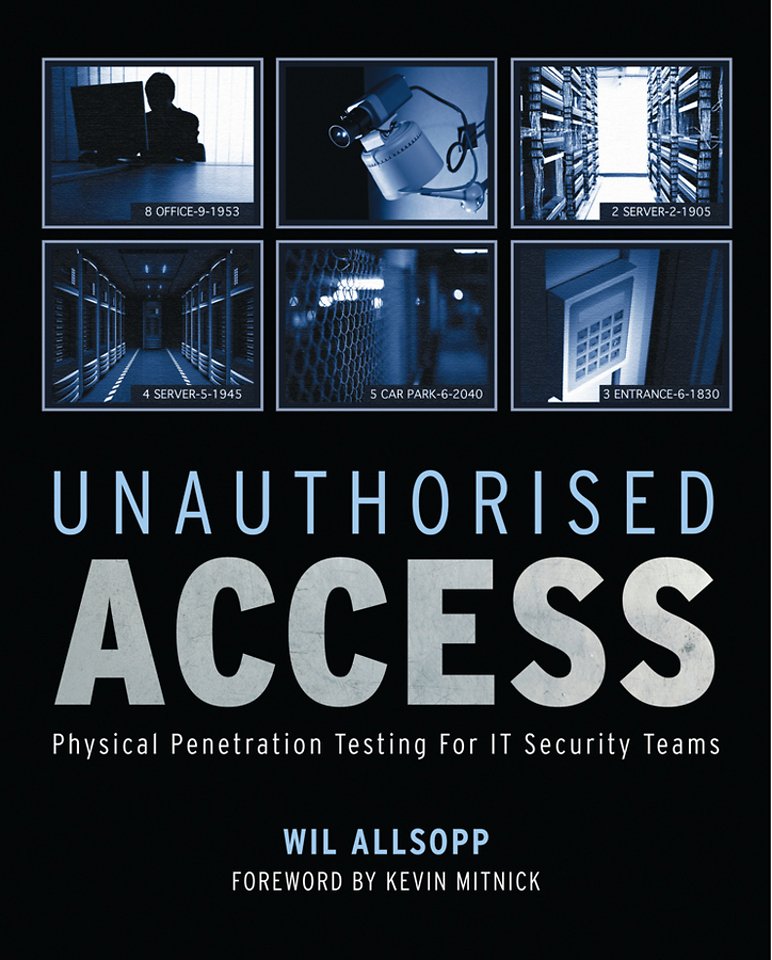
Unauthorised Access
Physical Penetration Testing for IT Security Teams
Samenvatting
The first guide to planning and performing a physical penetration test on your computer's security
Most IT security teams concentrate on keeping networks and systems safe from attacks from the outside-but what if your attacker was on the inside? While nearly all IT teams perform a variety of network and application penetration testing procedures, an audit and test of the physical location has not been as prevalent. IT teams are now increasingly requesting physical penetration tests, but there is little available in terms of training. The goal of the test is to demonstrate any deficiencies in operating procedures concerning physical security.
Featuring a Foreword written by world-renowned hacker Kevin D. Mitnick and lead author of 'The Art of Intrusion" and "The Art of Deception", this book is the first guide to planning and performing a physical penetration test. Inside, IT security expert Wil Allsopp guides you through the entire process from gathering intelligence, getting inside, dealing with threats, staying hidden (often in plain sight), and getting access to networks and data.
- Types of target vs level of anticipated response
- Dealing with guards
- Intelligence tradecraft, satellite imagery and in-depth information gathering
- Planting bugs adn covert wireless access points
- Hacking security cameras
- Stategic, tactical adn operational planning
- Defeating locks, elctronic keypads and other electronic access systems
- Social engineering-the weakest link
- Using your "Get Out of Jail Free" card
- Complying with local laws
- Attacking wireless networks
Specificaties
Inhoudsopgave
Acknowledgments
Foreword
1. The Basics of Physical Penetration Testing
2. Planning Your Physical Penetration Tests
3. Executing Tests
4. An Introduction to Social Engineering
5. Lock Picking
6. Information Gathering
7. Hacking Wireless Equipment
8. Gathering the Right Equipment
9. Tales from the Front Line
10. Introducing Security Policy Concepts
11. Counter Intelligence
Appendix A: UK Law
Appendix B: US Law
Appendix C: EU Law
Appendix D: Security Clearances
Appendix E: Security Accreditations
Index 277
Anderen die dit boek kochten, kochten ook
Net verschenen
Rubrieken
- aanbestedingsrecht
- aansprakelijkheids- en verzekeringsrecht
- accountancy
- algemeen juridisch
- arbeidsrecht
- bank- en effectenrecht
- bestuursrecht
- bouwrecht
- burgerlijk recht en procesrecht
- europees-internationaal recht
- fiscaal recht
- gezondheidsrecht
- insolventierecht
- intellectuele eigendom en ict-recht
- management
- mens en maatschappij
- milieu- en omgevingsrecht
- notarieel recht
- ondernemingsrecht
- pensioenrecht
- personen- en familierecht
- sociale zekerheidsrecht
- staatsrecht
- strafrecht en criminologie
- vastgoed- en huurrecht
- vreemdelingenrecht